Enterprise architecture is not merely about drawing diagrams or organizing systems. It is fundamentally about alignment, resilience, and defense. When security is treated as an afterthought, vulnerabilities become structural flaws that are costly to fix. The Open Group Architecture Framework (TOGAF) offers a robust methodology for embedding security principles directly into the fabric of enterprise design. By integrating risk management within the Architecture Development Method (ADM), organizations can construct environments that are secure by design rather than patched by reaction.
This guide explores how to operationalize security controls within the TOGAF framework. It moves beyond theoretical concepts to provide actionable steps for architects who need to balance innovation with protection. The focus remains on process, governance, and structural integrity, ensuring that every architectural decision accounts for potential threats.
🏗️ The TOGAF Foundation for Security
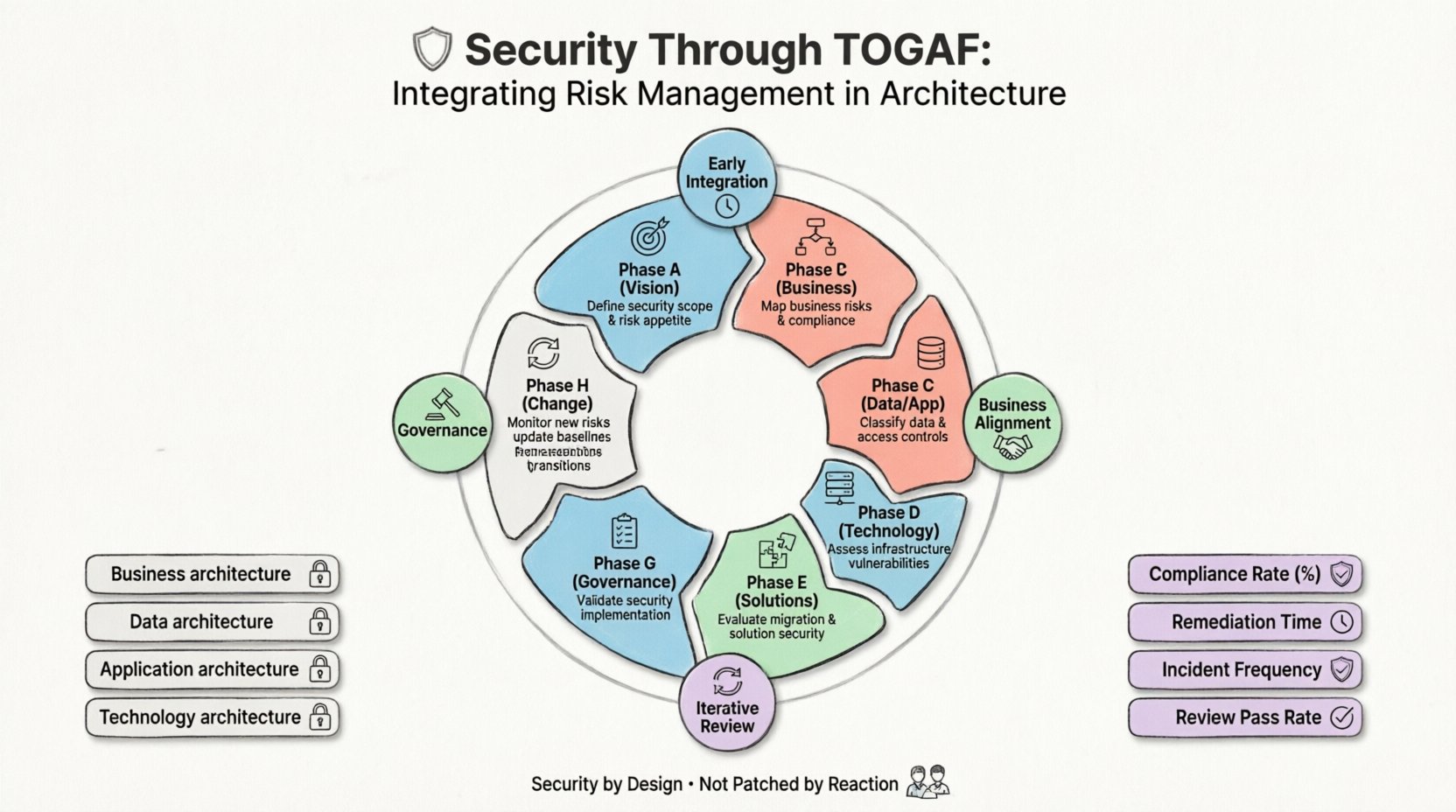
TOGAF provides a structured approach to enterprise architecture. While it does not prescribe specific security tools, it defines the architectural domains where security controls must reside. These domains include Business, Data, Application, and Technology architecture. Security is not a standalone silo; it must permeate each of these layers.
Integrating risk management requires a shift in perspective. Instead of viewing security as a checklist item at the end of a project, it must be a continuous constraint throughout the development lifecycle. This approach ensures that risk mitigation strategies are cost-effective and aligned with business goals.
Key principles for this integration include:
- Early Integration: Security requirements must be defined in the Preliminary Phase and Phase A.
- Business Alignment: Security risks must be understood in the context of business impact, not just technical failure.
- Iterative Review: Architecture is not static; risk profiles evolve, and the architecture must adapt.
- Governance: A formal mechanism is required to review security decisions against established baselines.
📊 Integrating Risk into the ADM Cycle
The core of TOGAF is the Architecture Development Method (ADM). This iterative process guides the creation of enterprise architecture. Each phase presents specific opportunities to assess and manage risk. Below is a structured view of how risk management fits into each stage of the cycle.
| Phase | Focus | Risk Management Activity |
|---|---|---|
| Phase A | Architecture Vision | Define security scope, stakeholders, and high-level risk appetite. |
| Phase B | Business Architecture | Identify business processes exposed to risk and compliance requirements. |
| Phase C | Data & Application | Map data flows, classify sensitivity, and define access controls. |
| Phase D | Technology Architecture | Assess infrastructure vulnerabilities and network segmentation needs. |
| Phase E | Opportunities & Solutions | Evaluate migration risks and solution security capabilities. |
| Phase F | Migration Planning | Plan secure transitions and manage project-level security risks. |
| Phase G | Implementation Governance | Ensure implemented solutions match the security architecture. |
| Phase H | Change Management | Monitor new risks introduced by changes and update baselines. |
This table highlights that risk management is not a single event. It is a recurring activity that spans the entire lifecycle. Architects must remain vigilant in each phase, ensuring that the security posture is maintained as the architecture evolves.
🔍 Detailed Phase Breakdown for Security Architects
Understanding the specific tasks within the ADM phases allows architects to operationalize security effectively. Below is a detailed breakdown of how to approach risk in the critical phases of the cycle.
Phase A: Architecture Vision
The journey begins by defining the security mandate. This involves establishing the Security Architecture Board (SAB) or integrating security representatives into the existing Architecture Board. The output of this phase should include:
- Security Principles: Rules that govern security decisions (e.g., least privilege, defense in depth).
- Risk Appetite Statement: A clear definition of how much risk the organization is willing to accept.
- Stakeholder Analysis: Identifying who is affected by security decisions and compliance obligations.
Phase B: Business Architecture
Security risks originate in business processes. If a process is inefficient, it may be bypassed, creating a security gap. In this phase, architects must:
- Map critical business functions to identify high-value assets.
- Analyze process flows to find points where data leaves trusted boundaries.
- Ensure that regulatory requirements (such as GDPR or HIPAA) are embedded in business rules.
Phase C: Information Systems Architectures
This phase covers Data and Application architectures. It is often where the most granular security controls are defined.
- Data Classification: Define levels of sensitivity (Public, Internal, Confidential, Restricted) and apply encryption standards accordingly.
- Access Control Models: Specify how users interact with applications (Role-Based Access Control vs. Attribute-Based Access Control).
- Application Security: Define requirements for secure coding, input validation, and session management.
Phase D: Technology Architecture
The physical and logical infrastructure supports the applications and data. Security here focuses on the platform.
- Network Segmentation: Design networks to limit lateral movement in case of a breach.
- Identity Management: Integrate Single Sign-On (SSO) and Multi-Factor Authentication (MFA) standards.
- Physical Security: Define requirements for data centers and edge devices.
🛡️ Gap Analysis and Security Remediation
Once the Baseline Architecture (current state) and Target Architecture (future state) are defined, a Gap Analysis is performed. In a security context, this analysis identifies the difference between existing controls and required controls.
The Gap Analysis should specifically look for:
- Missing Controls: Security mechanisms required in the target state but absent in the baseline.
- Weak Implementations: Existing controls that do not meet current security standards.
- Compliance Gaps: Areas where the current architecture fails to meet regulatory obligations.
Once gaps are identified, they must be categorized by risk severity. High-severity gaps often require immediate remediation, while lower-severity gaps can be addressed in future iterations. This prioritization ensures resources are allocated to the most critical threats first.
⚖️ Governance and Compliance Integration
Architecture is useless if it is not governed. TOGAF emphasizes the importance of the Architecture Contract and the Architecture Board. For security, this governance structure must be empowered to enforce compliance.
Security Architecture Board (SAB) The SAB acts as the oversight body for security decisions. Their responsibilities include:
- Reviewing architecture work products for security compliance.
- Approving exceptions to security policies when business needs dictate.
- Ensuring that migration plans adhere to security standards.
Compliance ManagementCompliance is often a driver for security architecture. However, compliance should not be the only metric. Security architecture should address risks that are not explicitly covered by regulations. This proactive approach protects the organization from emerging threats that legislation has not yet caught up with.
🔄 Implementation and Transition Governance
Phase G (Implementation Governance) and Phase H (Change Management) are critical for maintaining the security posture over time. An architecture document is a snapshot; the environment is dynamic.
Implementation Governance During implementation, architects must ensure that the solution being built matches the security design. This involves:
- Conducting security reviews at major milestones.
- Validating that configuration management processes prevent unauthorized changes.
- Ensuring that testing environments replicate production security controls.
Change Management Change is inevitable. Every change introduces potential risk. The Architecture Change Management process must include a security impact assessment. Before any change is approved, the following questions must be answered:
- Does this change expose new attack vectors?
- Does it alter data flow paths in a way that bypasses controls?
- Are the updated assets covered by the risk register?
📈 Measuring Security Maturity
How do you know the integration is working? Metrics are essential for demonstrating value and identifying areas for improvement. Architects should define Key Performance Indicators (KPIs) that reflect the effectiveness of the security architecture.
Recommended Metrics:
- Compliance Rate: Percentage of systems adhering to security baselines.
- Vulnerability Remediation Time: Average time taken to patch identified risks.
- Security Incident Frequency: Number of incidents per quarter, tracked by severity.
- Architecture Review Pass Rate: Percentage of projects passing security reviews on the first attempt.
These metrics should be reviewed regularly by the Architecture Board. Trends over time provide better insight than single data points. A rising trend in remediation time, for example, indicates a process bottleneck that needs architectural intervention.
🚀 Future-Proofing Architectural Decisions
Technology evolves rapidly. Cloud computing, remote work, and artificial intelligence introduce new vectors for risk. TOGAF architecture must be adaptable to these shifts.
Emerging Threat Landscape Architects must stay informed about the threat landscape. This does not mean following every news headline, but understanding the categories of threats relevant to the enterprise. For example, supply chain attacks require a different architectural control than insider threats.
Resilience Design Security is often about prevention, but resilience is about recovery. Architecture should assume that breaches will occur. Design decisions should focus on:
- Minimizing Blast Radius: Ensuring that a compromise in one segment does not compromise the whole.
- Automated Recovery: Designing systems that can restore integrity automatically.
- Redundancy: Ensuring critical security functions (like logging and authentication) are available even under attack.
🤝 Collaboration Between Security and Architecture
One of the biggest challenges in integrating security is organizational silos. Security teams often operate independently from Architecture teams. This separation leads to friction and inefficiency.
To succeed, these functions must collaborate closely. Security teams provide the threat intelligence and control requirements. Architecture teams provide the structural context and integration points. Joint workshops during the early phases of the ADM cycle are highly effective. They ensure that security constraints are understood before designs are finalized.
This collaboration also extends to procurement. When selecting vendors, security requirements should be part of the architectural criteria, not an afterthought. This ensures that third-party solutions align with the enterprise security architecture.
🧩 Common Pitfalls to Avoid
Even with a solid framework, mistakes happen. Understanding common pitfalls helps architects navigate the integration process more effectively.
- Over-Engineering: Implementing controls that are more complex than necessary. This creates maintenance burdens and reduces usability.
- Under-Documenting: Failing to document security decisions leads to knowledge loss when staff changes.
- Ignoring Legacy Systems: Focusing only on new builds while ignoring the risk profile of existing systems.
- Static Policies: Creating security policies that are not updated as the architecture changes.
Architects must remain pragmatic. Security is a trade-off between risk, cost, and usability. The goal is to achieve an acceptable level of protection without stifling business innovation.
🛠️ Practical Steps for Implementation
To begin integrating risk management into TOGAF, organizations can follow this roadmap:
- Establish the Framework: Define how TOGAF will be applied to security. Create a Security Architecture Extension to the standard framework.
- Train the Team: Ensure architects understand security concepts and risk management methodologies.
- Update Templates: Modify TOGAF artifacts (e.g., Architecture Definition Document) to include security sections.
- Launch Pilot: Apply the integrated approach to a single project to refine the process.
- Scale and Standardize: Roll out the approach across the enterprise based on lessons learned.
By following these steps, organizations can build a culture where security is a fundamental attribute of architecture, not an external constraint. This approach leads to more resilient systems and a stronger defense against evolving threats.
🔐 Summary of Key Takeaways
Integrating risk management into TOGAF requires a disciplined approach. It involves embedding security into every phase of the ADM cycle, from the initial vision to the ongoing management of change. The process relies on clear governance, collaboration between security and architecture teams, and a commitment to continuous improvement.
By focusing on the structural aspects of security, architects can create environments that are robust and adaptable. The result is an enterprise that can innovate with confidence, knowing that its foundations are secure. This alignment of security and architecture is essential for long-term success in a digital-first world.
Remember, security architecture is a journey, not a destination. The framework provides the map, but the organization must drive the vehicle. Regular reviews, updated risk registers, and active governance ensure that the architecture remains relevant and effective over time.