Enterprise Architecture serves as the blueprint for organizational structure and IT systems. However, a model without security considerations is incomplete. Security must be woven into the fabric of the architecture from the initial design stages. This guide explores how to embed security concerns directly into ArchiMate models, ensuring resilience and compliance without disrupting business agility.
🧩 The ArchiMate Framework Layers
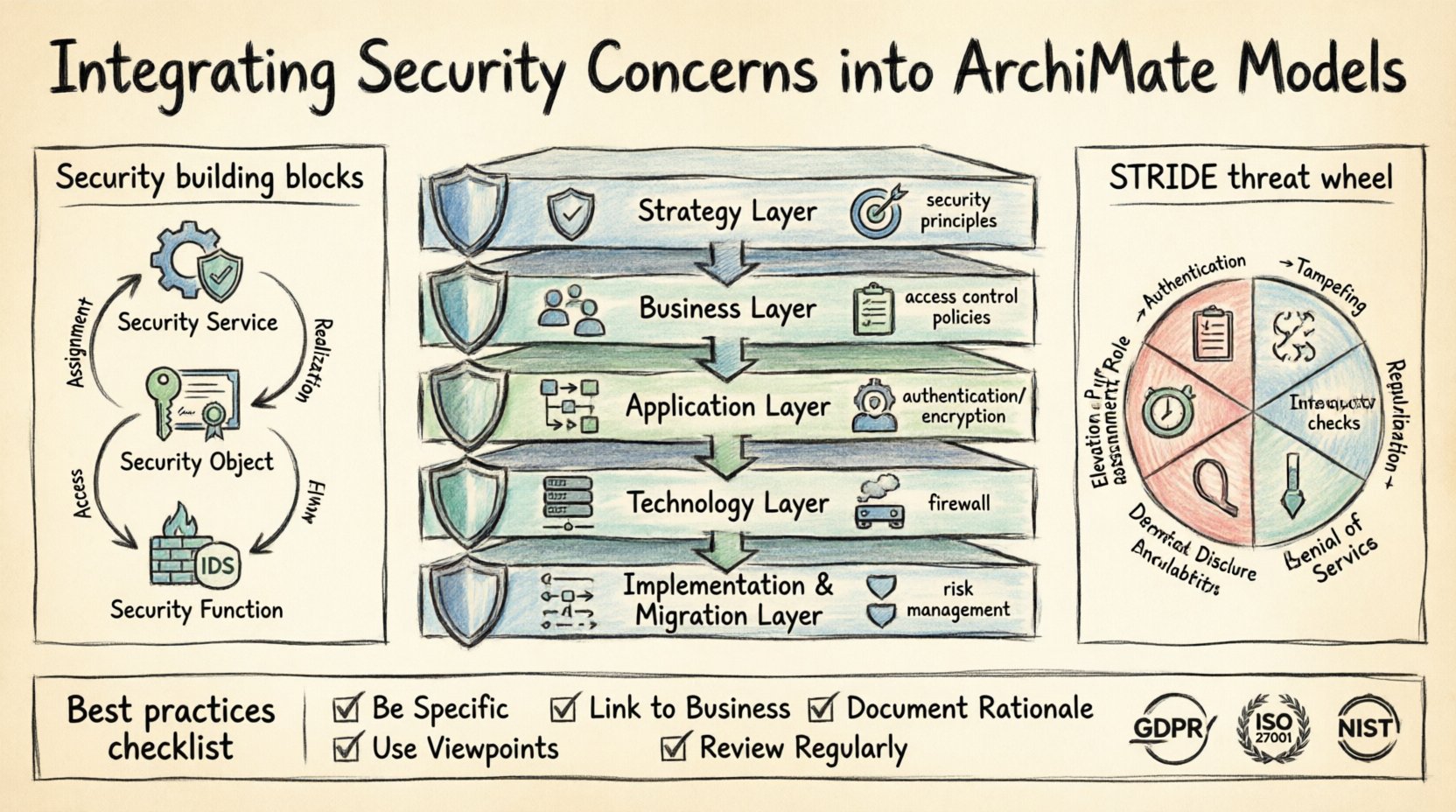
ArchiMate provides a structured view of an enterprise through several layers. Each layer represents a different level of abstraction. To integrate security effectively, one must understand how security artifacts map to these specific layers.
- Business Layer: Focuses on business processes, roles, and organizational structures. Security here involves access control policies and compliance requirements.
- Application Layer: Deals with software applications and their interfaces. Security concerns include authentication, authorization, and data encryption at the application level.
- Technology Layer: Represents the infrastructure. Security focuses on network security, physical security, and infrastructure hardening.
- Implementation & Migration Layer: Covers projects and initiatives. Security must be part of the deployment strategy and risk management.
- Strategy Layer: Defines goals and principles. Security principles guide the overall direction.
Integrating security requires mapping threats and controls across these layers. A vulnerability in the technology layer might compromise a business process. Therefore, a holistic view is essential.
🛡️ Security Concepts within the Standard
ArchiMate defines specific elements dedicated to security. Understanding these elements allows architects to model security explicitly rather than as an afterthought.
Security Objects
Security objects represent entities that provide security services. They can be:
- Security Service: A service that provides security functionality, such as authentication or encryption.
- Security Object: A passive element that holds security attributes, like a digital certificate or a key.
- Security Function: An active element that performs security operations, like a firewall or an intrusion detection system.
Security Relationships
Relationships define how security elements interact with other architectural elements. Common relationships include:
- Assignment: A security function is assigned to a business process.
- Realization: A security service realizes a security requirement.
- Access: A role accesses an application interface securely.
- Flow: Data flows between applications are secured.
Using these relationships ensures that security is not isolated but connected to the business value it protects.
🗺️ Mapping Security Concerns to Architecture
Different layers have different security priorities. The following table outlines how specific concerns map to the ArchiMate layers.
| Layer | Primary Security Concerns | Example ArchiMate Elements |
|---|---|---|
| Business | Access rights, compliance, fraud prevention | Role, Business Process, Business Object |
| Application | Authentication, integrity, confidentiality | Application Interface, Application Service, Security Service |
| Technology | Network isolation, physical access, host security | Device, Network, Security Function |
| Strategy | Security principles, risk appetite | Goal, Principle, Motivation Element |
When modeling, architects should ensure that every critical business process has a corresponding security control defined in the model. This visibility helps in audits and risk assessments.
🔍 Threat Modeling Integration
Threat modeling is a critical activity for identifying potential security weaknesses. Integrating this into ArchiMate models allows for a visual representation of risks.
Identifying Threats
Start by identifying the assets that need protection. In ArchiMate, these are typically Business Objects, Application Objects, or Technology Objects. Once assets are defined, consider threats:
- Unauthorized Access: Who can access the asset and how?
- Data Leakage: Where does data flow and is it encrypted?
- Service Disruption: What happens if a security function fails?
- Insider Threats: Are roles and responsibilities clearly defined?
Mapping Threats to Controls
For each identified threat, map a specific control. This creates a direct link between risk and mitigation. Use the Realization relationship to show how a Security Service realizes a security goal. This makes the rationale for security investments clear.
STRIDE in ArchiMate
The STRIDE model (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) can be adapted for ArchiMate.
- Spoofing: Map to Authentication mechanisms in the Application Layer.
- Tampering: Map to Integrity checks on Data Flows.
- Repudiation: Map to Audit Logs (Business or Technology Layer).
- Information Disclosure: Map to Encryption Services.
- Denial of Service: Map to Availability of Technology Layer components.
- Elevation of Privilege: Map to Role assignments and Access Rights.
By visualizing these threats, stakeholders can better understand the impact on the enterprise.
⚖️ Compliance and Governance
Regulatory compliance is often a driver for security architecture. ArchiMate supports this by linking security requirements to business goals.
Regulatory Mapping
Frameworks like GDPR, ISO 27001, or NIST can be represented as principles or requirements within the architecture.
- GDPR: Map data privacy requirements to Business Objects and Application Services.
- ISO 27001: Map security controls to Security Functions and Technology Layer components.
- NIST: Map risk management goals to the Strategy Layer.
This approach ensures that compliance is not just a checklist but an integral part of the system design.
Governance Processes
Security governance involves the processes that manage and control security. In ArchiMate, these can be modeled as:
- Review Processes: Scheduled audits of security configurations.
- Change Management: Security checks included in change requests.
- Incident Response: Defined workflows for handling security breaches.
Documenting these processes ensures that security is maintained over time, not just at the point of implementation.
🚧 Common Integration Challenges
While the benefits are clear, integrating security into ArchiMate models presents challenges. Recognizing these helps in planning mitigation strategies.
| Challenge | Impact | Mitigation Strategy |
|---|---|---|
| Complexity | Models become too large to manage | Use Viewpoints to separate security concerns from general architecture. |
| Security Silos | Security team works separately from architects | Include security architects in the modeling process from the start. |
| Lack of Standards | Inconsistent modeling of security elements | Define a standard library of security patterns and elements. |
| Dynamic Environments | Models become outdated quickly | Automate model updates where possible and link to real-time logs. |
| Stakeholder Buy-in | Security seen as a blocker | Demonstrate business value of security through risk reduction. |
Addressing Complexity
As models grow, they can become overwhelming. Viewpoints are the solution. Create specific viewpoints that focus only on security aspects. This keeps the general architecture clean while allowing security teams to drill down into specific concerns.
Addressing Silos
Collaboration is key. Security professionals should participate in architecture reviews. This ensures that security constraints are understood by business architects early in the lifecycle.
📊 Measuring Security Posture
Once security is integrated into the models, it is necessary to measure its effectiveness. Metrics help in understanding the current state and tracking improvements.
- Coverage: Percentage of critical business processes with mapped security controls.
- Compliance: Number of open compliance gaps identified in the model.
- Response Time: Time taken to update the model after a security incident.
- Risk Reduction: Quantitative measure of risk reduction achieved through architectural changes.
These metrics should be reported to governance bodies to ensure continued support for security initiatives.
🔄 Lifecycle Management
Security is not a one-time activity. It evolves with the enterprise. ArchiMate models should reflect this evolution.
Versioning
Maintain version control for security elements. When a security policy changes, the model should be updated to reflect the new requirement. This history helps in auditing past decisions.
Continuous Improvement
Regularly review security patterns. New threats emerge, and new technologies appear. The model should be flexible enough to incorporate new security functions or services as needed.
🔗 Connecting to Other Frameworks
ArchiMate is not the only framework in use. It often interacts with others like TOGAF or ITIL.
- TOGAF: Use ArchiMate to detail the Security Architecture in the Architecture Development Method (ADM).
- ITIL: Map security incident management processes from ITIL to ArchiMate business processes.
- NIST: Align security controls from NIST SP 800-53 with ArchiMate Security Objects.
Integration with other frameworks ensures a unified approach to enterprise management and security.
📝 Summary of Best Practices
To successfully integrate security into ArchiMate models, adhere to these practices:
- Start Early: Include security in the initial planning phases.
- Be Specific: Use specific ArchiMate security elements rather than generic notes.
- Link to Business: Always tie security back to business value or risk.
- Use Viewpoints: Manage complexity by separating concerns.
- Document Rationale: Explain why a control is in place using Motivation elements.
- Review Regularly: Ensure the model stays current with the environment.
Following these guidelines leads to a robust architecture that protects assets while enabling business goals.
🎯 Final Thoughts
Security architecture is a critical component of modern enterprise design. By utilizing ArchiMate, organizations gain a clear visual language to express security needs. This clarity facilitates better decision-making and more resilient systems. The effort to model security upfront pays dividends in reduced risk and smoother compliance audits. As the threat landscape evolves, the architecture must adapt. Keeping security at the center of the model ensures that the enterprise remains secure and competitive.
Architects who embrace this integration will find that security becomes an enabler rather than a barrier. It provides confidence to stakeholders and ensures that the organization can operate safely in a digital world.