Enterprise architecture serves as the blueprint for an organization’s structure, processes, and technology. However, a static blueprint is insufficient in a dynamic environment where threats evolve and regulations change. Integrating risk and compliance into the architectural framework ensures that resilience is designed into the system from the start. 🏗️ ArchiMate provides a standardized language to represent these complexities. By mapping risks directly to business capabilities, applications, and infrastructure, organizations can visualize vulnerabilities and align controls with strategic objectives. ⚖️ This guide explores the practical application of ArchiMate for modeling risk and ensuring compliance without relying on specific vendor tools.
🔍 Why ArchiMate for Risk Management?
Traditional risk registers often exist in isolation from the actual enterprise structure. This separation leads to blind spots where a critical business process might be supported by a legacy system with no documented security controls. ArchiMate bridges this gap by providing a layered view of the enterprise. 🌐
- Visualization: It transforms abstract risks into tangible architectural elements.
- Traceability: It links high-level business goals down to specific technology components.
- Communication: It offers a common language for architects, risk officers, and business leaders.
- Analysis: It allows for impact analysis when changes are proposed to the architecture.
Using a standard framework ensures that risk information is not lost during personnel changes or system migrations. It creates a living model where risk is a first-class citizen rather than an afterthought. 📝
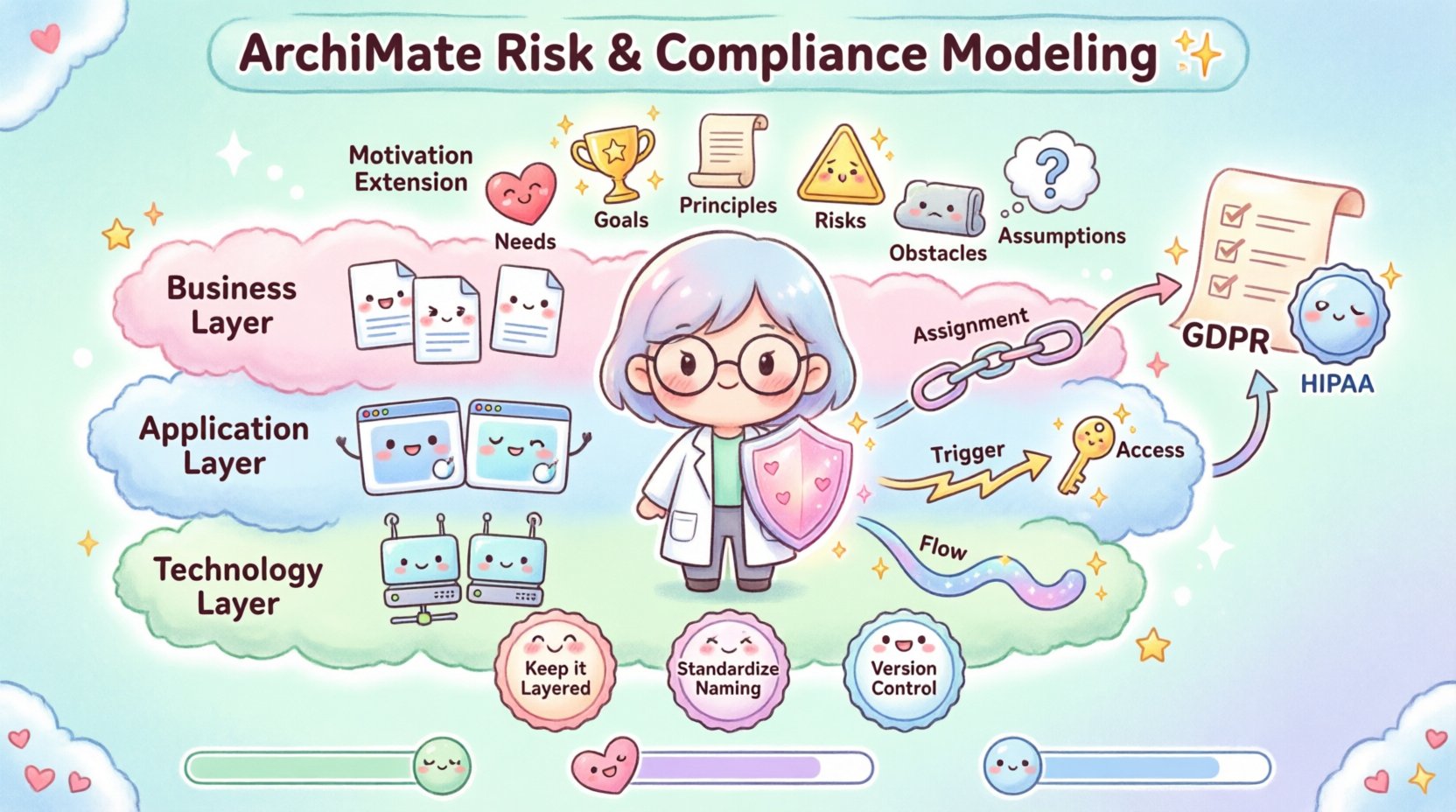
🧩 The Motivation Extension: The Core of Risk Modeling
The ArchiMate Motivation Extension is the most critical component for risk and compliance work. While the core layers (Business, Application, Technology) describe what the enterprise does, the Motivation layer describes why it does it and what stands in the way. This extension includes specific metamodel elements designed to capture uncertainty and requirements. 🎯
Key Elements in the Motivation Layer
- Needs: These represent the gaps between the current state and the desired state. In risk terms, a need might be the requirement to reduce data exposure.
- Goals: These are the desired outcomes. A goal could be achieving compliance with a specific regulation.
- Principles: These are the guiding rules. A principle might state that all customer data must be encrypted at rest.
- Risks: This is the direct representation of threats. A risk element captures the potential negative impact on an asset or process.
- Obstacles: These are barriers that prevent a goal from being achieved. An obstacle could be a lack of skilled personnel or budget constraints.
- Assumptions: These are conditions believed to be true. If an assumption regarding network stability is false, the risk model changes.
By modeling these elements, architects can explicitly show the relationship between a business driver and a specific risk. For example, a business goal of Customer Trust can be linked to a Risk element representing Data Breach. This linkage forces the architecture to address the risk to achieve the goal. 🤝
🏢 Modeling Risk in the Business Layer
The Business Layer represents the core value chain of the organization. Risks here often relate to process failure, regulatory non-compliance, or strategic misalignment. 📉
Business Elements and Risk
- Business Processes: Risks can be assigned to specific processes. If a process is critical, the associated risk must be higher priority.
- Business Roles: Risks often stem from human error or lack of oversight. Mapping risks to roles helps define accountability.
- Business Objects: These represent data or physical items. Risks here include loss, theft, or unauthorized modification.
- Business Services: These are the value delivered to customers. Service outages are a primary risk category.
Risk Mapping Strategy
When modeling risk in the business layer, it is essential to define the impact clearly. A risk element should be connected to the element it affects using the Assignment relationship. This indicates that the risk belongs to or is owned by that business element. 🔗
Additionally, the Realization relationship can show how a control (modeled as a Business Function) realizes a requirement to mitigate a risk. This creates a clear chain of evidence for auditors. 📋
| Business Element | Potential Risk | Architectural Impact |
|---|---|---|
| Order Processing | System Downtime | Affects Service Delivery |
| Customer Data | Data Breach | Affects Business Objects |
| Compliance Officer | Lack of Oversight | Affects Business Role |
💻 Application and Technology Layer Risks
While the business layer defines the value, the Application and Technology layers provide the foundation. Risks in these layers are often technical but have business consequences. 🖥️
Application Layer Risks
- Availability: Is the software accessible when needed?
- Integrity: Is the data within the application accurate and unaltered?
- Confidentiality: Is sensitive data protected from unauthorized access?
- Interoperability: Can the application communicate with other systems securely?
Architects can model these risks by linking them to Application Services or Application Components. For instance, a risk of SQL Injection might be linked to a specific Application Component. This allows the architecture to show exactly which component requires a specific security patch or firewall rule. 🔒
Technology Layer Risks
- Infrastructure Failure: Hardware breakdown or power loss.
- Network Security: Vulnerabilities in the network topology.
- Scalability: The inability to handle increased load.
- Dependency: Reliance on external vendors or third-party services.
Technology risks are often modeled against Device or Network elements. The Assignment relationship connects the risk to the device. The Access relationship can show how a risk (like unauthorized access) interacts with the technology element. 📡
⚖️ Compliance Mapping and Regulatory Alignment
Compliance is not a one-time event; it is a continuous state. ArchiMate helps maintain this state by mapping regulatory requirements to architectural capabilities. 📜
Steps for Compliance Modeling
- Identify Regulations: List all applicable laws (e.g., GDPR, HIPAA, SOX). Model these as Principles or Goals.
- Map to Capabilities: Link regulations to the business capabilities required to meet them.
- Define Controls: Model the technical and organizational controls needed to satisfy the regulations.
- Verify Coverage: Ensure every regulation has at least one supporting architectural element.
This approach prevents shadow compliance, where a department thinks it is compliant but the architecture does not support it. By visualizing the link, gaps become immediately apparent. If a regulation exists but no business function realizes it, the risk of non-compliance is high. 🚨
Managing Regulatory Changes
Regulations change frequently. When a new requirement is introduced, the architecture model can be queried to identify affected areas. 🔄
- Impact Analysis: Identify which business processes will need to change.
- Cost Estimation: Understand the resource implications of the new controls.
- Timeline Planning: Determine the sequence of updates required across layers.
This proactive stance reduces the cost of compliance and minimizes the risk of penalties. It turns compliance from a reactive burden into a structured architectural requirement. 🏗️
🔗 Relationships and Flows in Risk Models
The power of ArchiMate lies in its relationships. Risk modeling is not just about placing risk icons on a diagram; it is about showing how risks flow through the system. 🌊
Key Relationships
- Assignment: Shows ownership. Used to link a Risk to the Asset it threatens.
- Trigger: Shows causality. Used to show how an Event (Risk) triggers a Process (Response).
- Access: Shows interaction. Used to show how a Threat accesses a Resource.
- Flow: Shows movement. Used to show how Risk Information flows to Governance.
Consider a scenario where a Network Attack occurs. This is a Risk element. It Accesses the Firewall (Technology Element). If the firewall fails, it Triggers a System Breach (Business Event). This breach Assigns to the Reputation (Business Value). This chain of relationships tells a story of how a technical vulnerability becomes a business crisis. 📖
🛠️ Best Practices for Implementation
Creating a risk model is complex. Following established practices ensures the model remains useful and maintainable. 📚
- Keep it Layered: Do not mix layers unnecessarily. Keep business risks in the business layer and technical risks in the technology layer, but link them across layers.
- Standardize Naming: Use consistent naming conventions for risks, controls, and assets. This aids searchability and reporting.
- Version Control: Treat the architecture model like code. Track changes over time to see how risk posture evolves.
- Integrate with Governance: Ensure the risk model is reviewed during architectural decision-making meetings.
- Audit Regularly: Validate that the model matches the actual state of the enterprise.
🚧 Common Challenges and Solutions
Implementing ArchiMate for risk modeling is not without difficulties. Recognizing these challenges early helps in planning mitigation strategies. ⚠️
Challenge 1: Complexity Overload
Issue: Models can become too detailed, making them unreadable.
Solution: Use abstraction levels. Show high-level risks on the main view and drill down into details only when necessary.
Challenge 2: Data Silos
Issue: Risk data often lives in spreadsheets separate from the architecture repository.
Solution: Export risk data into the modeling tool. Ensure a single source of truth is established.
Challenge 3: Maintenance Burden
Issue: Models become outdated quickly.
Solution: Assign ownership. Specific architects should be responsible for updating specific domains of the model.
📊 Measuring Success and KPIs
How do you know the risk modeling effort is working? Key Performance Indicators (KPIs) provide the metrics needed to demonstrate value. 📈
- Coverage Rate: Percentage of critical assets that have associated risks modeled.
- Control Mapping: Percentage of risks that have identified and implemented controls.
- Update Frequency: How often the risk model is reviewed and updated.
- Incident Correlation: Ability to trace real incidents back to modeled risks.
Tracking these metrics helps demonstrate the return on investment for the architecture function. It shows that the model is not just a diagram, but a functional tool for decision-making. 🎯
🔄 Sustaining the Model Over Time
An architecture model is not a finished product. It is a living asset that must evolve with the enterprise. 🌱
To sustain the model, integrate it into the change management process. Whenever a new project is initiated, the architecture team should review the risk model to ensure the new changes do not introduce unacceptable risks. This continuous integration ensures that risk remains visible throughout the lifecycle of the architecture. 🔄
Furthermore, training is essential. Architects and business stakeholders must understand how to read and interpret the risk model. If the model is not understood, it cannot be used effectively. Workshops and documentation should be provided to ensure organizational alignment. 🤝
🔮 The Future of Risk Modeling
As technology evolves, so do the risks. Automation and AI introduce new complexities. ArchiMate provides the structure to model these future risks as they emerge. 🔮
- Automation: Automated scanning can update the model with new vulnerabilities.
- AI Risks: New risk types related to algorithmic bias or data privacy.
- Cloud Dynamics: Risks associated with shared responsibility models in the cloud.
By maintaining a flexible and robust modeling framework, organizations can adapt to these changes without losing visibility. The goal is to build a system that is resilient by design, capable of withstanding shocks and adapting to new threats. 🛡️
📝 Summary of Key Takeaways
Integrating risk and compliance into ArchiMate transforms the architecture practice. It moves beyond describing what exists to explaining what could go wrong and how to prevent it. 🧭
- Use the Motivation Extension to link goals to risks.
- Map risks across all layers: Business, Application, and Technology.
- Leverage relationships to show flow and impact.
- Keep the model updated and integrated with governance.
- Measure success through clear KPIs.
This approach ensures that risk management is not a separate silo but an integral part of how the enterprise is designed and operated. It empowers leaders to make informed decisions with a clear view of the potential downsides. 🏛️